The Competitive Advantage Most Small Manufacturers Are Sleeping On

Some manufacturers are winning contracts their competitors aren’t even being considered for, they’re passing customer audits without scrambling, and they’re renewing cyber insurance without surprises. How? They’re adding “cybersecurity readiness” to a list of credentials that sets them apart in procurement conversations and made a decision their competitors haven’t made yet.
Cybersecurity for small manufacturers is still widely treated as a cost to minimize or a compliance box to check. The manufacturers pulling ahead are treating it as something else entirely: a business asset. A differentiator. A reason customers choose them over the shop down the road.
Here’s what’s driving that shift, and how your business can get ahead of it.
Why Cybersecurity Pressure on Manufacturers Is Only Growing
Manufacturing has become one of the most targeted industries for cyberattacks. According to IBM’s 2024 X-Force Threat Intelligence Index, manufacturing was the most attacked industry for the third consecutive year.
The reasons are specific to how manufacturing works. Operational technology (OT): the networked systems that run your machines and production floor, was largely built before cybersecurity was a design consideration. Just-in-time production schedules mean downtime is expensive fast, which makes manufacturers more likely to pay ransoms. Supply chain relationships mean a breach at one supplier can ripple across an entire customer’s operation.
Larger customers understand this. And they’re starting to act on it.
Procurement teams at mid-size and large manufacturers are increasingly asking their suppliers documented questions about cybersecurity practices. Some are requiring it as a condition of doing business. The manufacturers who can answer those questions confidently — with evidence, not just assurances — are the ones getting shortlisted.
That’s the opportunity. The pressure is real. The gap between manufacturers who’ve addressed it and those who haven’t is widening. And right now, the bar to be on the right side of that gap is still low enough for a smaller shop to clear it.
What “Getting Ahead” Actually Looks Like
Strong cybersecurity in a smaller manufacturing business doesn’t look like a Fortune 500 security operations center. It looks like clarity, ownership, and a handful of practices done consistently well.
The businesses that do this well share a few things in common.
Someone owns it
In most smaller manufacturers, cybersecurity belongs to no one specifically, which means it belongs to everyone loosely and it gets done inconsistently. The businesses that get ahead write a name next to “cybersecurity” on their org chart. That person doesn’t need to be a technical expert. They need to coordinate the work, ask the right questions, and make sure nothing falls through the cracks.
Cybersecurity accountability starts with a name, not a department.
They know where their risk actually lives
Most smaller manufacturers don’t have a clear picture of where their technology systems connect, where their data lives, or which vendors have access to their network. A cybersecurity assessment changes that. It helps you understand your terrain well enough to protect it.
The manufacturers who handle incidents well aren’t always the most secure. They’re the most prepared. They’ve thought through what happens if the floor goes dark, who they call, what they do in the first hour, and how they communicate with customers. A plan written in advance takes minutes to execute. A plan written during a crisis takes hours.
Their people are part of the defense
Cybercriminals don’t compromise networks by outsmarting technology. They compromise them by tricking people. From a phishing email that looks like a vendor invoice, a phone call impersonating IT support, to a link in a shipping notification. Your team is your first line of defense, and regular, practical training is what makes that line hold.
This doesn’t require expensive software or all-day seminars. In fact, awareness training once a year, or at the start of employment ends up feeling like a chore that’s easy to forget instead of small learning opportunities that help to create a ‘Culture of Security’ in the organization, and something your team thinks about the same way they think about safety on the floor.
How Cybersecurity Opens Doors for Small Manufacturers
The practical business benefits of strong cybersecurity show up in places manufacturers don’t always expect.
It wins contracts
Larger customers are increasingly asking suppliers to complete security questionnaires, provide documentation of their practices, or demonstrate compliance with recognized frameworks like the National Institute of Standards and Technology (NIST) Cybersecurity Framework. Manufacturers who can answer those questions clearly, and back it up with evidence, move through procurement faster. Those who can’t get stuck, or get passed over.
Being able to say “here’s how we protect your data and our shared supply chain” is a competitive statement. Most of your competitors can’t say it yet.
It makes insurance work better
Cyber insurance is increasingly difficult and expensive to obtain without demonstrable security practices in place. Carriers are asking harder questions at renewal, tightening coverage terms, and in some cases declining to renew policies for businesses that can’t document their controls.
Manufacturers with strong cybersecurity practices get better coverage at better prices. They also don’t get surprised at renewal time. That’s a real financial advantage that compounds over time.
It protects your production — and your reputation
A ransomware attack that stops your production line doesn’t just cost you the ransom. It costs you the production hours, the penalty clauses in your contracts, the customer relationships that get strained, and the reputation damage that follows a public incident. Manufacturers who invest in cybersecurity before an incident are protecting all of that — not just their data.
And the manufacturer who has a real answer when a customer asks “what would happen to our orders if you had a cyber incident?” are the ones customers trust with larger, longer-term contracts.
CMMC: A Compliance Requirement That’s Also a Business Signal
For manufacturers in the defense supply chain, Cybersecurity Maturity Model Certification (CMMC) is the most formal version of a trend happening across the entire manufacturing sector: customers requiring proof, not promises, when it comes to cybersecurity.
CMMC 2.0 is finalized and prime contractors are already flowing requirements down to their suppliers. If your business touches a Department of Defense contract anywhere in the chain, you likely have CMMC obligations in your current contracts, or they will be added soon.
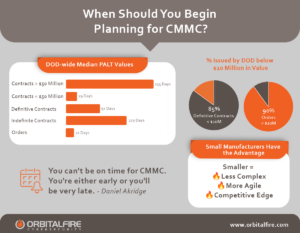
CMMC has three levels. Most smaller manufacturers fall under Level 1 or Level 2. Level 1 covers 17 foundational practices: controlling who has access to your systems, protecting against malware, and basic operational hygiene. Level 2 aligns with the 110 security requirements in NIST SP 800-171, covering access control, incident response, risk assessment, and more. Level 2 is where most defense suppliers land, and where the real work happens.
The path to certification requires documentation: a System Security Plan (SSP) that maps your controls, a Plan of Action and Milestones (POA&M) that tracks your gaps, and for Level 2, a third-party assessment from a Certified Third-Party Assessment Organization (C3PAO). None of this is out of reach for a smaller manufacturer, but it requires a managed, intentional approach.
Here’s the opportunity: most manufacturers in the defense supply chain haven’t started. The ones who move now build the documentation, the practices, and the credibility ahead of the deadline crunch. They also build something their non-certified competitors can’t claim: a provable, independently verified security posture. In defense contracting, that’s a significant differentiator. Even if you’re not yet certified but are making your way through CMMC readiness, that often can make the difference when it comes to winning a contract. And the practices that get you to CMMC compliance make your business stronger in every other customer relationship too.
As an RPO (Registered Practitioner Organization – a CMMC certification) OrbitalFire helps smaller manufacturers navigate every step of the CMMC journey — from gap assessments and documentation to full compliance readiness. We offer a complete suite of NIST 800-171 and CMMC services with a clear roadmap and pricing that doesn’t require an enterprise-sized budget.
Where to Start
You don’t have to solve everything at once. The manufacturers who get ahead aren’t doing everything perfectly, but they’re doing the right things intentionally, in the right order.
- Get an assessment. You can’t close gaps you haven’t mapped. A cybersecurity assessment gives you a clear picture of where you stand in your technology, your processes, and your people, and tells you where to focus first.
- Put a name next to cybersecurity. Assign ownership internally. It doesn’t require technical expertise; it requires accountability and follow-through.
- Build an incident response plan. Know who you call, what you do, and how you communicate if something goes wrong. Written in advance, it takes minutes to execute. Written during a crisis, it takes hours you don’t have.
- Train your people. Regular, practical training changes behavior. Annual checkbox training does not.
- Understand how your OT and IT connect. If your production equipment shares a network with your business systems, that connection is a risk worth understanding and addressing.
- If you’re in the defense supply chain, start your CMMC journey now. CMMC 2.0 went into effect November 2025 but most smaller manufacturers haven’t made much progress. The manufacturers who move early have the advantage.
The OrbitalFire Perspective
We specialize in cybersecurity for smaller businesses. including manufacturers navigating OT risk, supply chain requirements, CMMC compliance, and the simple reality that a single incident can set a smaller operation back months.
We do all the hard work for you: assessments, training, compliance roadmaps, monitoring, and planning. Our certified, values-driven team is laser-focused on your results.
The manufacturers pulling ahead of their competitors on cybersecurity aren’t waiting for a breach to take it seriously. They’re building the advantage now.
Frequently Asked Questions
Can cybersecurity really be a competitive advantage for a small manufacturer?
Yes — and increasingly so. Larger customers are asking suppliers harder questions about cybersecurity before awarding contracts. Manufacturers who can answer those questions with documentation and evidence move through procurement faster and earn more trust. Strong cybersecurity also means better cyber insurance terms, lower risk of costly downtime, and a reputation for operational reliability. The bar to differentiate is still low enough for a smaller shop to clear it, but that window won’t stay open indefinitely.
Why are small manufacturing businesses targeted by cybercriminals?
Smaller manufacturers sit at the intersection of several factors attackers look for: high-value operations that can’t afford downtime, production systems that weren’t designed with cybersecurity in mind, supply chain relationships that create access to larger targets, and lean teams without dedicated security resources. Attackers aren’t looking for the biggest target; they’re looking for the most accessible one. Size is not protection.
Does my MSP handle my cybersecurity?
Not entirely, and most MSPs will tell you that. Your MSP keeps your technology running: systems online, software updated, employees productive. Cybersecurity goes further. It covers your people, your processes, your access controls, your compliance requirements, your incident response plan, and your ability to detect and respond to threats. In fact, 80% of cybersecurity has nothing to do with technology. MSPs keep you running. A dedicated cybersecurity partner keeps you secure. These are complementary services, not the same one.
What is CMMC and does it apply to my manufacturing business?
Cybersecurity Maturity Model Certification (CMMC) is a compliance framework required for businesses in the U.S. defense supply chain. If your business contracts with the Department of Defense, or supplies to a prime contractor that does, you likely have CMMC obligations. Most smaller manufacturers fall under Level 1 or Level 2 of the framework. Even if CMMC doesn’t apply to you directly, the practices it requires are the same practices that build competitive advantage in any customer relationship.
How do I start improving cybersecurity at my manufacturing business?
Start with an assessment. Before you can close gaps, you need to know where they are in your technology, your processes, and your people. From there, prioritize ownership (put a name next to cybersecurity), employee training, an incident response plan, and an understanding of how your production and business systems connect. You don’t have to solve everything at once. You do have to start. OrbitalFire works exclusively with smaller businesses to make that process straightforward and built around your actual operation.









